Update: The patent is dead now! After you're done reading my rant,
check out this post on how to
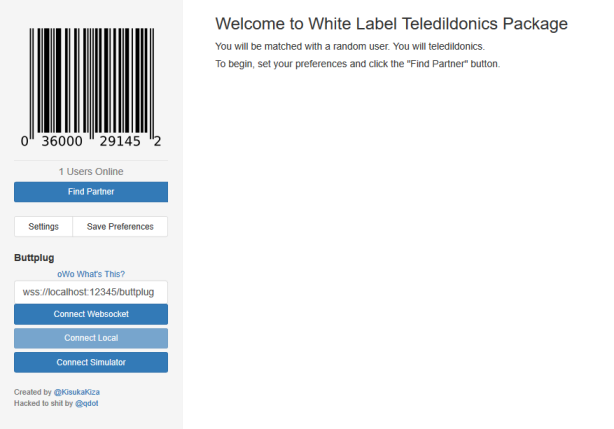
set up your own teledildonics server.
The 268 Teledildonics patent, fucking up internet buttplugs in the US
since 1997, expires in a few hours.
My earliest mention of it seems to be from a project announcement I
wrote in
2005,
so I've been sitting with this for at least 13 years. The open source
teledildonics network mentioned in that post never even got started,
though now I have Buttplug, which is far more
useful.
If you want a brief timeline of what this patent has fucked up, check
out this article on
FutureOfSex,
as well as the recent
followup
that includes interviews of those affected by the lawsuits. I also
recommend reading David Parisi's fantastic work on RealTouch
history.
Finally, there's an article from today by Maxine Lynn, an Actual IP
Lawyer, about the expiration..
After you've done all that, check out this article on
VirtuaDolls,
one of the lesser covered losses of the patent wars.
Except VirtuaDolls wasn't a victim of the 268 patent, it's another
patent on interactive technologies. If you think the end of the 268
patent is the beginning of a sex tech revolution, you're gonna have a
Real Bad Time once you find out about all of the provisional patents
filed throughout the last few years. Modern sex tech companies have
set up an environment of mutually assured legal destruction while
making damn sure no new players will rise just because as of
2018/08/17 you can UDP some vibrations to someone somewhere else and
not have to pay a license for it in the US.
Don't get me wrong, the expiration of the 268 patent is fantastic,
even though it's sad it wasn't brought down through invalidation
against prior art like the Wachspress
device
or the Safe Sex Plus. This is (or, well, was) a patent making it
difficult to run a business around a nebulous definition of remote
communication, stifling innovation and possibly not allowing
important, useful products to make it to market.
However, this is all about US patents. Everything mentioned so far has
been about blocking products in one country of 350 million or so
people. That leaves ~194 countries and ~7.1 billion other people left
to build toys and do whatever with them and maybe just not sell them
in the US.
They're definitely out there doing just that.
Ok, not all ~7.1 billion of them, but at least a few.
Companies have been building networks and toys in Europe and Asia.
Vibease got out of the TZU 268
lawsuit
because they're mostly selling to Indonesia, Malaysia, and Singapore
(and that is one hell of a marketing feat, considering some of the
conservative cultures throughout those countries). If you search for
"bluetooth vibrator" on
AliExpress,
it's quite obvious this patent hasn't stopped China from manufacturing
all sorts of absolutely wild shit and packaging it with remote control
capabilities. Japan had Segment in the late
2000s,
has Vorze/Rends now, and probably other companies I'm not even aware
of.
None of the products I've encountered have universal praise. Most of
them find niche communities of use and that's it.
I'm not aware of any killer app of sex toys or teledildonics that the
US is missing out on right now. I'm not sure it requires US innovation
to come up with one, either. People in all countries fuck, otherwise
there wouldn't be people in all countries. The US doesn't have a
monopoly on sexy times, or engineering, or engineering of sexy times.
RealTouch is an example that comes up pretty often when talking about
268 patent losses, but RealTouch was around for years before they
released RealTouch Interactive and ran into patent issues. It's not
like they had a stranglehold on the market that whole time, or that
they were a household name when they were forced out. There's enough
people who think we're going to get Jude Law style sex robots next
year to fuel constant media articles around it. Patent or no, sex tech
remains a fairly unknown field with a small amount of inexperienced
companies just putting out what they can 'cause neither the
manufacturer nor customers know better, and the customers don't have
much choice of what to buy otherwise.
Not only that, teledildonics is remote control of sex toys. What
about local control? I would argue that the sex tech engineering
community (myself included) sucks at making interfaces period. The
Teledildonics patent held up other people controlling your toy, but
sometimes you don't have that other person, and there's local
interfaces that might be interesting. It's not fair to say that 268
stopped all innovation, but masturbation just doesn't sell as well
either.
Even when companies have the money to license the patent in the US,
they implement remote control but fuck up on privacy and data storage.
This is why there are class action suits against Standard Innovation
and Lovense.
Stifling innovation means many people don't want to put in the work
because they can't turn their idea into money. In a capitalist society
where you pay for your own healthcare, that's literally a question of
life and death. It leaves the industry to those that got in early,
that start out well off enough to fend off lawsuits, or who are
weirdos like me who will happily produce shit and release it for free.
One less roadblock in one country with an admittedly large market
presense is good, but it's not a panacea. I'm not even sure it's going
to fix much.
Not gonna act like I don't have dreams, though.
I'm probably more realistically optimistic about sex tech now than
I've ever been.
Despite the patent there's a lot of commercial companies building
products of varying levels of quality now. We've got projects like
Open Privacy doing work to create trustable,
private networks, and Internet Of Dongs
helping companies not fuck up with the security of sensitive data
storage.
The biggest blow of the 268 patent, for me, was the loss of potential
of companies like Comingle, and that's why I'm
glad there's one less weapon for assholes to clear the market with. If
we want the singing/dancing/fucking perfectly humanoid sex robots all
of the trash media articles say we're getting next year (we're not),
we have to start somewhere and work slowly from there.
Comingle was a good start. They wanted to give people a platform to
build their own sexual experience without having to start from
scratch. I believe we need more educational sex tech, more ways for
people to explore their own wants and needs. I want the producers
of that tech to worry about ethics and privacy and ergonomics and how
we communicate intimacy and consent through the sewer pipes of the
internet. I want them free of the burden of winding through a forest
of shitty patents, in the US or anywhere else.
I realize a lot of people are angry that RealTouch made a good blowjob
robot and you can't get it anymore due to patents and maybe that'll be
less of a problem now, but I'd much rather have hundreds or thousands
of people educated about sex tech and how to ethically, properly
create it. Then they can go on building the next hundreds or thousands
of [insert act of sex or intimacy] robot instead.
The 268 patent held back mass market sex tech. While I think there's a
lot wrong with mass market sex tech, Buttplug
wouldn't exist without it. That said, don't wait on the mass market to
free up enough to make your own solutions viable as a product. Sex is
extremely personal act, and the internet has proven that almost no one
is alone in the way they enjoy it. The most vibrant, interesting
sexual communities online never gave a fuck about 268 or any other
patent. The energy and excitement of those communities is part of why
this blog is still around after all of these years.
Fuck patents. Fuck products. If you're interested in sex tech, find
your community. If you have the skills, build with them. Communicate
with those building things, because it turns out engineers don't know
everything and usually need guidance. Produce one-offs via
AdaFruit and
Shapeways and
Tindie if you have the funds, or set up
Patreons or Indiegogos
to do small runs, not crazy huge launches. If you're afraid of
possible legal repercussions, reach out, to me, to lawyers like
Maxine Lynn. You may have less to
worry about than you think, but you should do your homework
nonetheless.
If you make money, fantastic. If you break even, great. Hopefully you
don't lose money on it, but that's definitely the situation to plan
for.
Communicate and publish, if you can. Make sure your projects live on
somehow. Please tell me when you do so I can yell about your work on
here, on twitter, on
mastodon, wherever. If you don't want
to be the face of it, that's fine, I can work with you on ways to
anonymize things. I cannot begin to convey how much interesting,
personal DIY sex tech we've lost due to issues of shame and "just
anonymously throwing things on a message board thread" that gets
pushed down due to history then the board dies.
Don't expect this patent expiration to just solve sex tech and flood
the market with perfect products. No one gets magically better at
producing sex tech at midnight tonight. There's still a fuckton of
work to put in.